Cyberattacks on healthcare providers continue to plague the industry. Over the past two years, 45 percent of healthcare organizations have experienced a data breach and there is not an end in sight.
Healthcare organizations are improving their defenses, but challenges remain. The Ransomware Task Force (RTF), a collaborative of security experts from government and industry, recently reported: The majority of organizations globally are still underprepared to defend against or recover from a ransomware attack.
Meanwhile, the U.S. Department of Health and Human Services (HHS) closed out 2024 by issuing a Notice of Proposed Rulemaking (NPRM) to modify the Health Insurance Portability and Accountability (HIPAA) Security Rule. The aim is to increase cybersecurity protections for electronic protected health information (ePHI).
The focus on updating the rule follows a recent report from the HHS Office of Inspector General. The report examined the enforcement of the HIPAA Privacy Rule by the Office for Civil Rights (OCR). In the report, the OIG noted that the HIPAA audit was too narrowly focused to effectively assess ePHI protections. The report called out that the audit only assessed 8 of 180 HIPAA Rules and only two were related to the Security Rule, with nothing related to physical and technical safety.
The OIG report noted that (current) OCR oversight of its HIPAA audit program was not effective at improving cybersecurity protections at covered entities or business associates.
There are about twenty updates proposed in the new HIPAA Security Rule including:
- Specific Risk Analysis – New requirements would include a written assessment that contains:
- An up-to-date technology asset inventory and a network map. This would require tracking the flow of ePHI across all systems and require annual updates or updates when significant changes to the organization’s operations or environment occur.
- Identification of all reasonably anticipated threats to confidentiality, integrity, and availability of ePHI
- A list of possible vulnerabilities and predisposing conditions to the regulated entity’s relevant electronic information systems.
- An assessment of the risk level for each identified threat and vulnerability, based on the likelihood that each threat will exploit the identified vulnerabilities.
- More Technical Safeguards – A select list of the suggested technical updates is below.
- Encryption of ePHI at rest and in transit.
- Multi-factor authentication, advanced encryption protocols and mandatory vulnerability scanning every six months.
- Network segmentation separates mission critical assets into discrete network segments to minimize lateral movement by threat actors after initial compromise.
- Separate technical controls for backing up and recovering ePHI to ensure data integrity and availability.
- A compliance audit at least annually to ensure compliance with the Security Rule requirements.
The complete NPRM can be viewed or downloaded here.
What do the newly proposed HIPAA rules mean for healthcare providers?
These new requirements come with a hefty costs for provider organizations to update technologies and processes. However, the cost of not acting is not only high, but also endangers critical infrastructure, patient safety and opens the door for other harmful consequences.
This means it is more important than ever to think through an enterprise data management strategy and to consolidate the IT footprint as much as possible to reduce risk, remove unnecessary costs and to be prepared for the future.
One step that organizations can take immediately is to know what technology assets they have in use.
The OCR proposes to require regulated entities to conduct and maintain an accurate and thorough written technology asset inventory and a network map of its electronic information systems and all technology assets that may affect the confidentiality, integrity or availability (CIA) of ePHI.
The Technology Asset Inventory requirements in the proposed HIPAA rule includes six areas:
- All physical devices and systems including servers, computers, mobile devices, and medical devices.
- Software. All applications and software programs used to process, store and transmit ePHI. Includes operating systems, databases, and other relevant structures.
- Network components. All devices and components such as routers, switches, firewalls, and other infrastructure that supports the network.
- Data storage locations. All locations where ePHI is stored. Includes on-prem data centers, cloud storage and backup systems.
- Endpoints. All endpoints that access the network, such as workstations, laptops and other devices that are connected to the organization’s applications.
- Security measures. Details of the security measures in place to protect each asset, such as encryption, access controls and anti-malware software.
How can legacy data management support healthcare providers in meeting the new HIPAA Rule?
It’s a well-known fact that legacy systems are a leading risk factor for security incidents. We’ve outlined the six major security risks lurking in legacy systems.
The best protection against the risks from keeping legacy systems up and running is to:
- Utilize this tool we developed to create an inventory of legacy systems to support decision making and guide the legacy data management plans.
- Create (or update) the organization’s legacy data management strategy.
- Consolidate legacy data into an active archive like HealthData Archiver® which helps the organization meet regulatory requirements that can include record retention of up to 30 years or more.
- Decommission legacy EHR and ERP systems to remove risk factors and realize security, cost and other benefits.
Adopting strong legacy data management practices helps organizations be prepared for the expanded HIPAA Security Rule and other regulatory updates like the Health Data, Technology and Interoperability (HTI-2) proposed rule from the Dept. of Health and Human Services through the Office of the National Coordinator for Health Information Technology. The Harmony Healthcare IT team continues to innovate and update its solutions with features to support expanding needs such as clinical image exchange, multi-factor authentication and more.
Are you looking for a legacy data management partner that is focused on the future?
Reach out to our trusted team at Harmony Healthcare IT.
Additional references:
The proposed rule, press release and fact sheet. Comments are due by March 7, 2025. The current regulatory text for review is here.




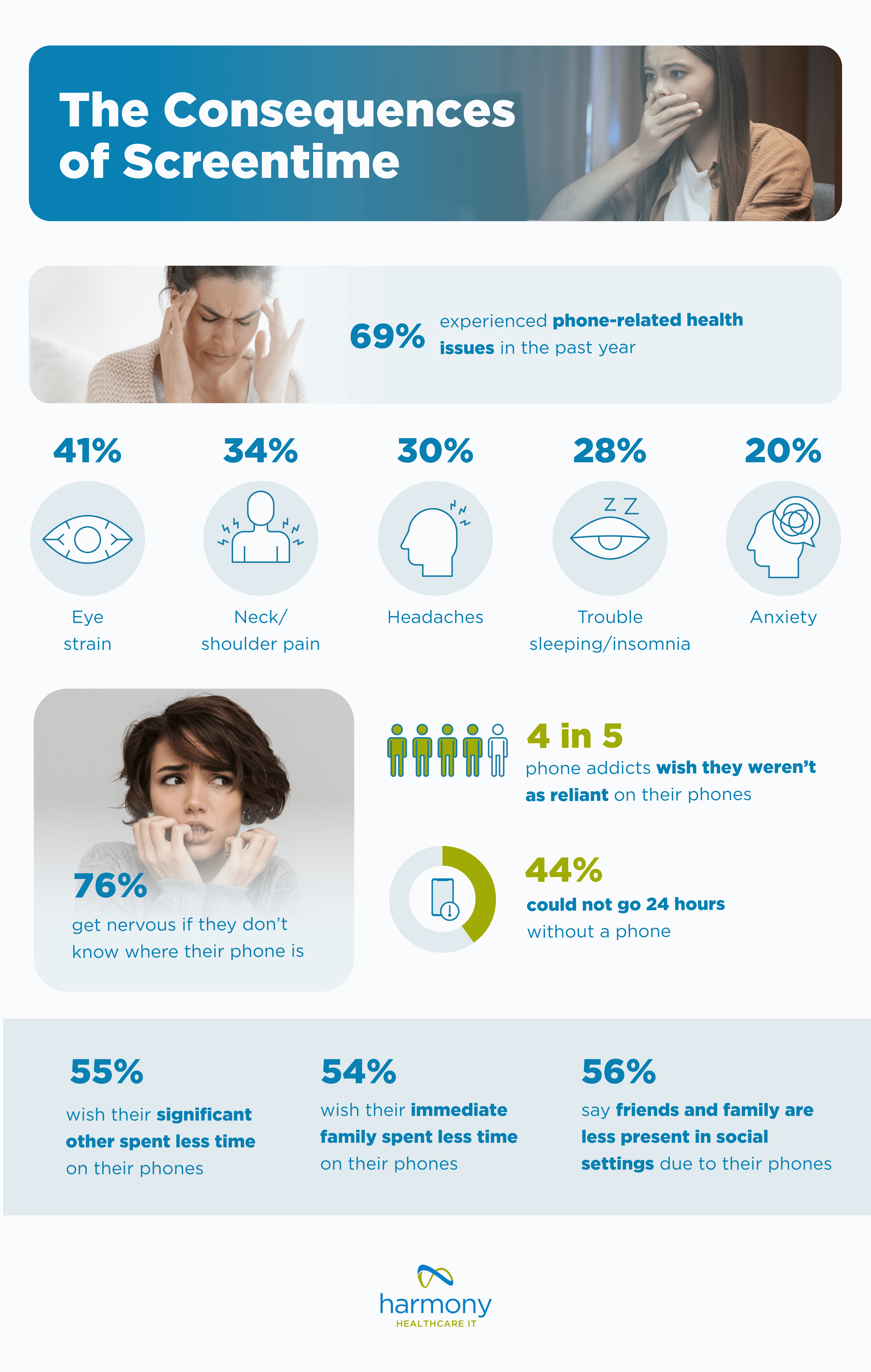
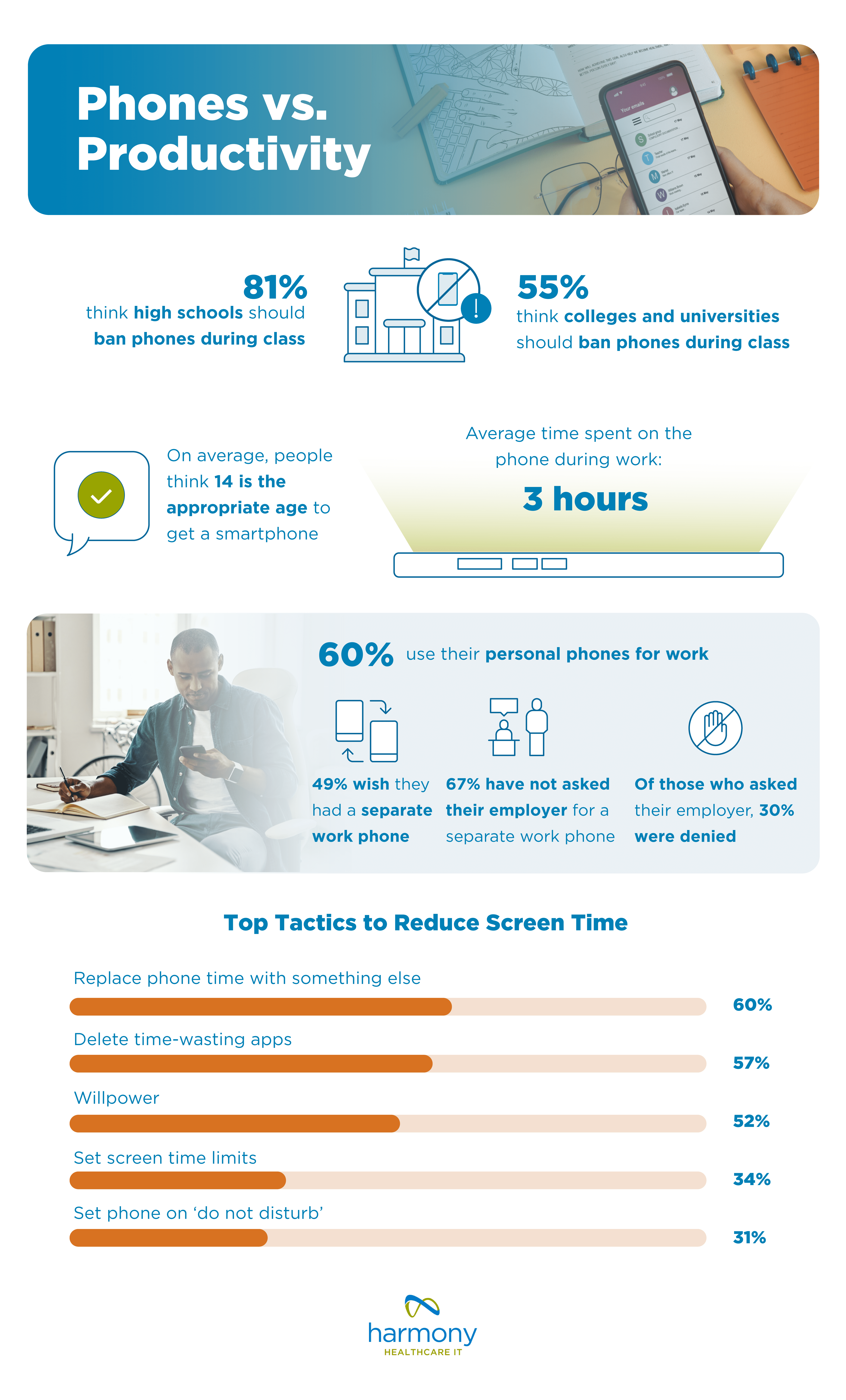
 Americans spend an average of 5 hours and 16 minutes per day on their phones – a 14% increase from the 4 hours and 37 minutes people reported spending on their phones in 2024. Age plays a significant role, with Gen Z spending the most time on their phones, and Baby Boomers spending the least. How much time does Gen Z spend on their phone? Gen Z spends 6 hours and 27 minutes on their phone every day while Baby Boomers spend a little over 4 hours (which is still double the recommended limit).
Americans spend an average of 5 hours and 16 minutes per day on their phones – a 14% increase from the 4 hours and 37 minutes people reported spending on their phones in 2024. Age plays a significant role, with Gen Z spending the most time on their phones, and Baby Boomers spending the least. How much time does Gen Z spend on their phone? Gen Z spends 6 hours and 27 minutes on their phone every day while Baby Boomers spend a little over 4 hours (which is still double the recommended limit).